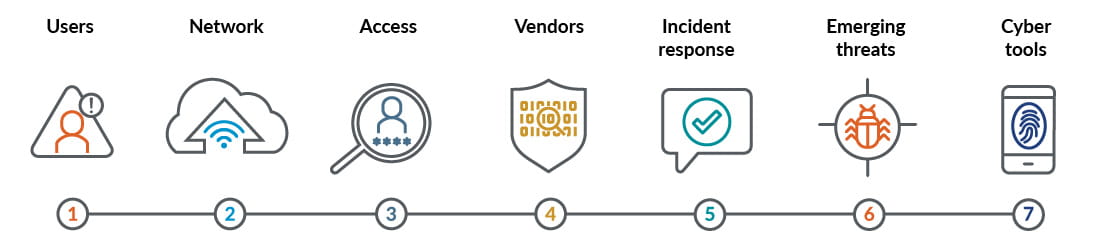
Seven-point cybersecurity assessment: Identify your organization’s digital risks
- View In
- English
- 日本語
Are you working aggressively to protect your information systems and data, yet you’re still unsure of the effectiveness of your security controls?
These seven areas can shed light on how well you’re protecting the confidentiality, availability, and integrity of your information and IT assets, as well as compliance with various security and privacy regulations.
By strengthening these seven areas, you can prevent a cybersecurity incident from happening to your company.
1. Users: Train users & assess their risks
To perform their day-to-day functions, users are provided with access to your systems and data. These users can present a high risk to your organization, mostly from negligent practices such as weak passwords, indiscriminate downloading, phishing attacks, etc. It’s important you properly onboard, train, and hold your users accountable for their actions on information systems. This includes regular review of your onboarding and termination processes, system access rights, and user awareness training.
2. Network: Monitor & defend against evolving cybercrime
Your network is an interconnected group of systems that communicate and operate together on a technology infrastructure, including software, hardware, services, and other resources. Your network should be hardened through proper configuration and separation from public networks. It should also be periodically tested and continuously monitored to help detect and defend against potential cyber incidents.
3. Access: Review user permissions annually
Access refers to your user’s permissions and how they are restricted based on roles and responsibilities. Permissions should be annually reviewed and access levels granted, revoked, or changed per duties.
4. Vendors: Protect vendor data
Third-party service providers support your organization’s operations with IT services. Your organization should have vendor oversight to ensure no vendor security breaches take place and any data shared with vendors is duly protected. This includes a process for vetting vendors and their roles and responsibilities and reviewing vendor contracts for cybersecurity disclosure notification language and confidentiality clauses.
5. Incident response: Prepare for, respond to, & recover from cyberthreats
Your organization should have a tested process and plan in place to respond to a cybersecurity incident. Without a formal plan, your customers, employees, IT systems, and even brand can be negatively impacted. Your incident response team should include representatives from all major departments and internal or external legal counsel.
6. Emerging threats: Defend against phishing, malware, & data loss
Cybersecurity attacks are constantly evolving, and the consequences are becoming more severe. Common threats like phishing, malware, ransomware, and denial of service (DoS) attacks can disrupt or cause damage to your system, network, or data and harm your organization’s reputation. You should proactively evaluate your organization’s safeguards to ensure you’re protected from these common cyberattack strategies, emerging threats, and risks associated with compliance.
7. Cyber tools: Solutions to defend, detect, & respond to cyberthreats
Many organizations are transforming the way they conduct business by adopting new tools and technologies — and expanding their digital presence in the process. To offset cybersecurity risk associated with changing business practices, you need tools and solutions in place. Selection and implementation of the proper cyber solutions is only the beginning; these tools need to be regularly evaluated and monitored to ensure you can effectively defend against, detect, and respond to cyberthreats.
This thought-provoking exercise is crucial; without it, you simply can’t know if you have the correct controls to diminish the perceived risks. With our help, you can get ahead of any unforeseeable problems by developing strategies, from the results of our seven-point cybersecurity assessment, to strengthen the areas that present the most risk to your organization. Contact us to start the assessment process now.




