An email from your company’s help desk goes out to all your staff, instructing them to click a link to update their password. Only it’s not really from your help desk — it’s from a cybercriminal — and an untrained staff member clicks the malicious link. The next thing you know all your organization’s files are locked with a note telling you that if you don’t pay up they’ll release sensitive data. That’s a ransomware attack and if you’re not training your staff to identify and avoid phishing emails your organization is at huge risk.
There are three factors that often lead to crime: need, opportunity, and knowledge. COVID-19 has created a perfect storm. Economies worldwide are in shambles leaving millions out of work — the resulting economic pressure creates the need. The pandemic has also driven people out of public spaces and into their homes leading to a dramatic increase in use of technology. This creates the opportunity for criminals who conduct their activities online. The third factor — knowledge — is the easy part. Anyone with Google access and sufficient motivation can get it. Now all cyber scammers need is a target, and that’s potentially you, your staff, and your business.
COVID-19-era phishing tactics
COVID-19 has presented enticing opportunities for cyberattacks and recent scams tend to have these things in common: They often look like they’re coming from an authoritative entity, they’re unexpected, they suggest the “issue” is immediate, and they ask you take an action such as clicking a link or giving out your personal information. Phishing attempts are often in the form of:
- An email from your office’s technology department asking you to update your password.
- An automated phone call claiming you owe money to the IRS and need to pay urgently.
- Texts from delivery services saying a package needs your immediate attention.
These types of scams are increasingly common and it’s likely you’ve received at least one since the start of the pandemic.
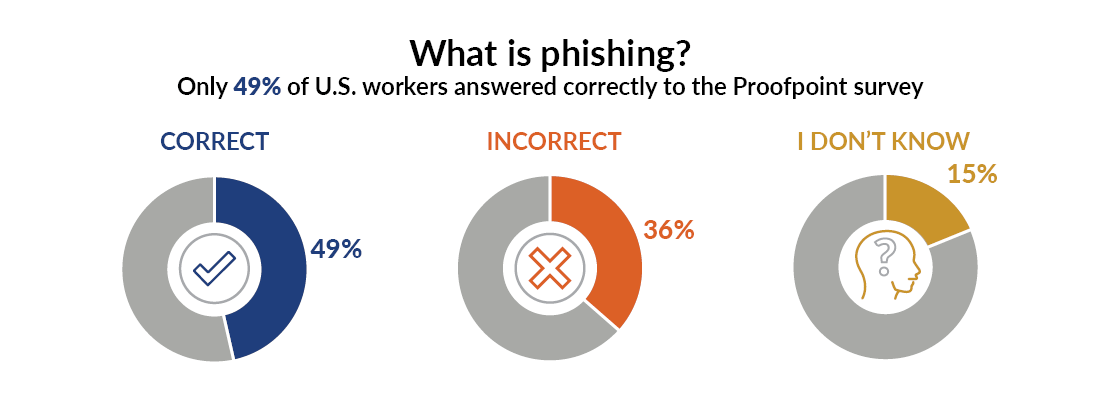
Despite phishing’s pervasiveness, awareness is still shockingly low. One recent survey reports just 49% of U.S. workers are even familiar with the term “phishing,” and another reports that only 31% of workers receive cybersecurity training at work. Given these statistics it’s understandable that awareness is as low as it is.
What’s at risk when you don’t train for cybersecurity awareness
Phishing is a numbers game. Hackers send out massive amounts of text, emails, and other communications to their targets, and if just a few take the bait, that’s all they need. If you’re one of the two-thirds of companies that don’t conduct cybersecurity awareness training, your staff — and therefore your entire company — is more vulnerable to the numbers game.
The key risks of a successful phishing attack are:
- Business interruptions: Cybercriminals can take your organization offline or steal its data. Such an interruption in business operations could result in delayed delivery of goods and services, severe financial challenges, and damage to your reputation. While the extent of the interruption and resulting damage will depend on the type of attack and your level of cyber resilience, a key component to a successful outcome is your ability to fortify against an attack upfront by training your staff to recognize Phishing and other hacking attempts.
- Loss of sensitive data: Customers will rapidly lose trust in a company that falls victim to a cyberattack but nothing damages trust like the loss of data. Your company likely holds private personal information about customers or clients and it’s your duty to protect it. If you fail to do so, your business may never recover. Why would anyone trust you with their sensitive data if they don’t think it’s safe in your hands? You could also be slapped with heavy fines for failing to adequately protect the data.
- Ransomware: Ransomware is a popular form of cyber-attack that hackers can conduct by simply purchasing a “launch and go” kit online. Once a successful phishing attempt allows them into your system criminals can lock down your data until you agree to pay a hefty sum. In addition to the business interruption it can also create serious technical and ethical challenges.
Start with cybersecurity awareness training
Given the severe consequences of a cyberattack your organization’s budgeting plans should include cybersecurity protections. In addition to properly-trained security staff and the necessary cybersecurity software, you should have two more things in place to handle the “human error” issue: staff awareness training to prevent against attacks, and an emergency plan to head off an attack before it reaches a critical stage.
The training program for your staff should include how to recognize phishing attempts and risky actions to avoid. Off-the-shelf training solutions are available that cover these scenarios along with practice exercises and quizzes. Many are customizable to your organization. This kind of training should be conducted at least annually with reminders sent to refresh staff throughout the year.
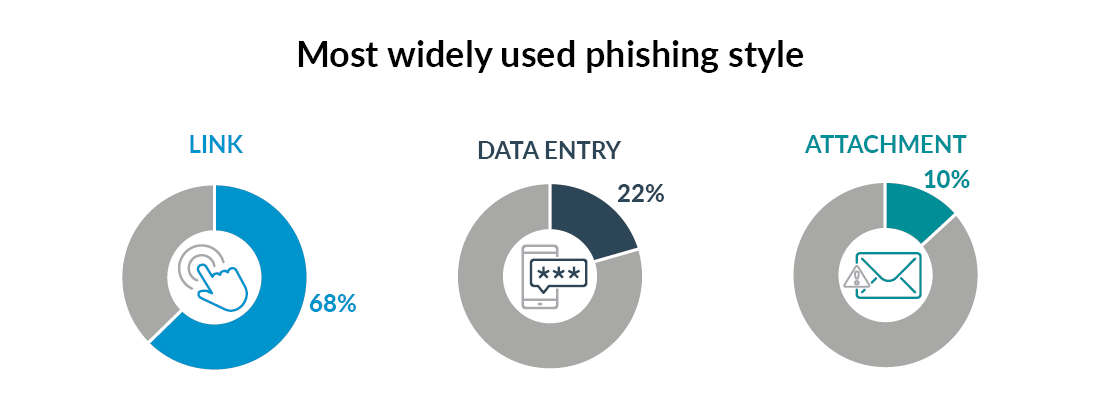
Alongside the training we recommend the IT department conduct phishing tests by sending staff fake phishing emails a few times during the year to test their awareness. The emails should have varying levels of obviousness; for example one could be rife with spelling errors from a clearly suspicious email address asking staff to urgently click on a link. Another could look just like an email from your CEO asking them to open an attachment quickly. The point is not to “trick” your staff but to help them learn how to spot phishing attempts in the context of their daily work.
In addition to general training, organizations should explain internal policies relating to sensitive information. For example let staff know the help desk would never send a request asking them to email a password. Or explain a policy that staff will always receive a heads-up if the organization plans to have an external source send an email with an embedded link.
Emergency plans
While prevention is essential, even the most well-trained staff member is still capable of human error. That’s why emergency plans are so important: If you know what to do, you can stop an attack before it gets out of control. For example, if your organization is hit with a ransomware attack and you immediately implement the emergency plan you can quickly disconnect systems, isolate the area that the scammer gets access to, and get a warning message out to staff right away. Without a plan, you can lose precious time scrambling to figure out what to do. A well-thought-out plan could be the difference between a small interruption and a complete disaster.
Don’t delay your cybersecurity plans
Getting started with cyber awareness can be challenging and time-consuming so don’t wait. The increased opportunity for cybercrime isn’t going away anytime soon. The good news is that you don’t have to have all the cybersecurity expertise in-house and you don’t have to create the plans on your own. An expert partner can help you get the right protections, training materials, and emergency preparedness plans in place. For more information give us a call.





