In today's digital landscape, the threat of cybersecurity incidents looms large, often originating from the most unexpected places. These incidents can catch your organization completely off guard, affecting all aspects of your business. At the core of protecting your company lies a fundamental truth: it's not just the responsibility of your IT department. It requires a unified commitment from your entire organization, from board leadership and executive teams through every business unit. But the stakes are even higher. Your existing customers, potential clients, and dedicated staff expect nothing less than robust protection. A single cyber event can leave a lasting scar on your brand's reputation, and it doesn't stop there. The financial implications can be significant, impacting your bottom line in ways you never anticipated.
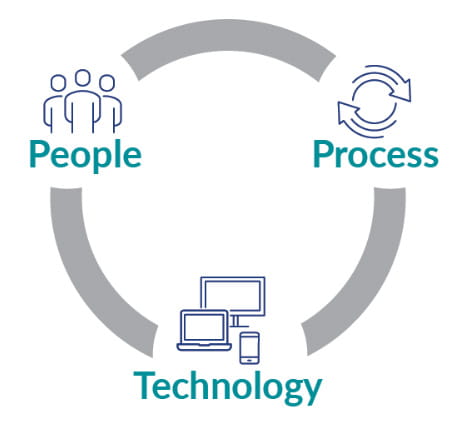 By focusing on the three vital components driving your organization — people, processes, and technology — we can help you adopt a comprehensive and proactive approach to safeguarding your organization. Our goal is to assist you in achieving a holistic cybersecurity strategy that leaves no stone unturned.
By focusing on the three vital components driving your organization — people, processes, and technology — we can help you adopt a comprehensive and proactive approach to safeguarding your organization. Our goal is to assist you in achieving a holistic cybersecurity strategy that leaves no stone unturned.
From conducting thorough risk assessments to developing robust incident response protocols, our methodology covers the entire spectrum of cybersecurity. We go the extra mile by employing cutting-edge testing techniques that replicate the tactics used by real-world cybercriminals. This risk-based approach ensures that the confidentiality, integrity, and availability of your systems and data remain uncompromised while adhering to the necessary security and privacy regulations.
Our unwavering commitment is to equip your entire organization with an understanding of the complex cybersecurity challenges you’ll likely face. By doing so, we empower your people, enhance your processes, and fortify your technology against both known and unforeseen threats. Rest assured, we are dedicated to providing you with practical and cost-effective solutions that enable you to make informed decisions and to protect what’s most important to you and your clients and customers.
With our comprehensive range of services and expertise, we’re dedicated to supporting your organization's cybersecurity endeavors, enabling you to achieve resilience and peace of mind in an ever-evolving digital landscape.
After a rigorous accreditation process covering policies, processes, and competencies, our cybersecurity experts achieved CREST certification for penetration testing in December 2024. After fulfilling training and volunteering requirements in data privacy and cloud security systems, our cybersecurity experts achieved CSA Trusted Cloud Provider certification and entered the STAR program in March 2025. In late 2024, the Cybersecurity Maturity Model Certification program became the official DOD program for protecting Controlled Unclassified Information (CUI), and our experts are certified to navigate these extensive cybersecurity requirements to assist you in your compliance remediation journey.














.jpg?mw=722&hash=C4C4544E5CB98C0C0149C2D8A0E12D0C)

