Recently, Chris Roberts, a cybersecurity researcher and pro hacker, found himself in hot water after sending a tweet about a plane’s security systems.
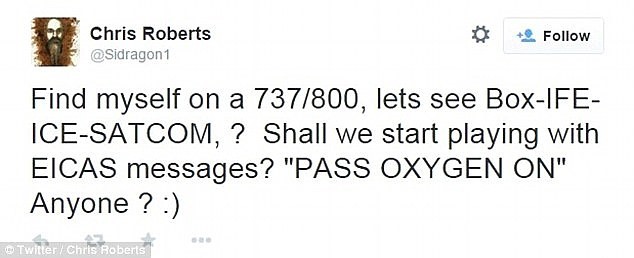
Chris tampered with the plane during a United Airlines flight to Chicago. The plane went on to Philadelphia where the FBI inspected it and found evidence of damage and tampering with the Seat Electronic Box below Chris’s seat and the seat in front of him. From Chicago, Chris took a connecting flight to Syracuse where the FBI was waiting for him. He was taken in for questioning, and his laptop, hard drive, and other gear were confiscated by the FBI. United Airlines later banned him from the airline altogether.
Chris told the FBI that he’s hacked into planes more than 20 times. He claims that he’s even managed to control an aircraft engine during flight by accessing the Thrust Management System and forcing one of engines into a sideways climb. I find this hard to believe, since no one — including the pilot, monitoring systems, or Federal Aviation Administration — noticed it. Since the FBI let him go, I assume he didn’t truly hack the system because he would have been in violation of federal statutes.
Chris has also claimed that he was able to adjust the temperature on a NASA space station. You can listen https://www.youtube.com/watch?v=Vl7TlSOEeQM to him talking about it at a conference in 2012. NASA spokesman, Dan Hout, denied that anyone, including Chris Roberts, has hacked any space station.
According to Chris, hacking these systems is fun for him, but tampering with real planes and space stations could cost lives — something he seems willing to sacrifice to identify vulnerabilities.
Most airlines and manufacturers have pointed out that flight control systems are separate from inflight entertainment systems. However, as with cars, airplanes are configured by a digital data bus that allows a common, wired path two-way communication between multiple devices and units instead of a separate wire connecting each system. According to aviation electronic specialists, systems are configured to only receive commands from pre-programmed sources. While Chris’s story might not be credible, he raises an important point that planes could be vulnerable to hacking. He probably was able to connect to the plane’s entertainment system through the seat’s electronic box. He’s a highly talented cybersecurity expert and is quite capable of using his laptop and hacking tools via a modified ethernet cable to the electronic components below his seat.
Perhaps the most alarming thing Chris has said is that he’s accessed a plane’s systems by using default user IDs and passwords. Leaving the default ID and password simple to guess means any security features installed can be easily bypassed. This can be fixed by not using a default admin password and providing each system with its own admin ID and password or using authorized token devices for admin logins.
In light of these occurrences, the FBI and TSA issued an alert to airlines advising them to be on the lookout for evidence of tampering or network intrusions. During my next flight, I wouldn’t be surprised to hear the flight attendant say during pre-flight announcements, “Federal law makes it illegal to tamper with any aviation electronic systems ….”
I support the United Airlines decision to ban Chris from future flights. I’m a frequent flier, and I definitely don’t want anyone on my plane tampering with the oxygen or any other electronic system that can impact our safety. Cybersecurity experts are a great asset in identifying vulnerabilities before the bad guys; however, they can’t put people’s lives, or our critical infrastructure, in danger to do so.
This content originally appeared at crainsdetroit.com and is part of a special blog series on cybersecurity.





